Trending
-
News
Achieving the Sublime in Email Security: Announcing Our $20M Series A Investment
-
Close ups
Cloud Captains: How Assaf Rappaport and His Extraordinary Co-Founders Built the World’s Fastest-Growing Company
-
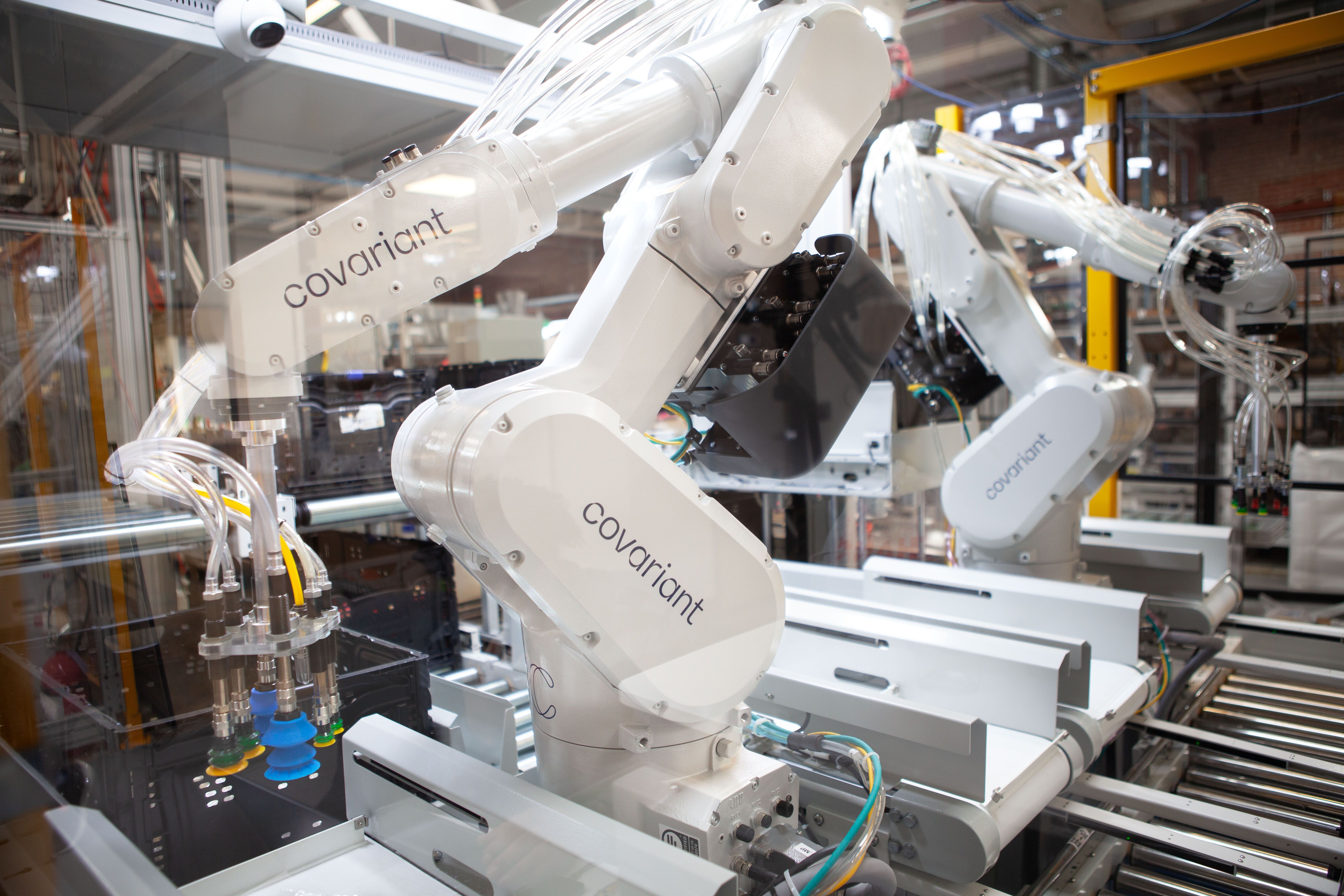
The Rise of Vertical AI
-
News
Nourish raises $35M to help millions live longer, healthier lives
-
Insights
Healthcare's "Why Now" Moment
- News
- Insights
- Close Ups
- Conversations